SOLUTIONS
Healthcare
Symmetry delivers comprehensive Data+AI security solutions that prioritize the protection of patient information, addressing the unique challenges faced by healthcare organizations. With an increasing number of cyber threats targeting sensitive patient data, Symmetry ensures your data remains secure and compliant.
Symmetry for Healthcare

Protection
Secure private identifiable and health information effectively, preventing it from being leaked, exploited, or sold.



Compliance
Ensure strict adherence to stringent healthcare regulations like HIPAA, HITECH, HITRUST, and French HDS.



Innovation
Embrace innovation without compromising on security, even amid increasing cyber risks due to COVID-19 and cloud adoption.



Efficiency
Automate data management and security operations across hybrid cloud environments with Symmetry’s single-console solution.



Visibility
Gain comprehensive and accurate insights into where data is stored, who has access to it, and how it is used.



Resilience
Minimize potential risks and exposures by providing detailed visibility and control over data across multiple cloud environments.



Leveraging Symmetry to Ensure High-Level Data Protection
Crossbeam, a partnerships ecosystem platform, adopted Symmetry’s DataGuard to enhance their data protection capabilities. Facing challenges in monitoring data access and usage, Crossbeam needed a solution that could automate these processes efficiently and cost-effectively. DataGuard provided Crossbeam with the ability to precisely monitor who accesses their data and how it is used, significantly aiding in SOC2 audits and improving data security from the inside out. This approach was particularly effective in Crossbeam’s AWS cloud environment, aligning with their “security-from-the-data-out” philosophy. The implementation of DataGuard not only streamlined compliance and security processes but also demonstrated its effectiveness during tests by quickly detecting and responding to unauthorized actions.



Industry
Software as a Service



Size
200+ Employees, Private



Team
Chris Castaldo, CISO



Chris Castaldo, Crossbeam CISO, and his team are committed to keeping their business, customers, partners and, most importantly, their data safe from cyber threats. The team sought a single solution that could show exactly who and what has access to data, put guardrails around that data, and ultimately could ensure protection of data against cyber threats. They had processes in place to do this arduous task manually, but it required the use of valuable time, money, and resources that could be reallocated to other critical business tasks. They needed a robust data security posture management (DSPM) solution that could tell them at any time where their data was, who had access to it, and what it was being used for.
The team’s ultimate goal was to ensure all their data was protected, while also having the ability to see who has access to what data at any given time. This was especially important for SOC2 audits. They also wanted to be able to determine, from a hacker’s point of view, which of their applications could be compromised. They had evaluated products that could determine some of this from an outside perspective, but they wanted something that really started from the inside—that is, security from the data out. Why wait for a cyber threat actor to get to the data before deploying protections? Crossbeam wanted a product that started with data protection.
Chris and his team evaluated a few different data security posture management solutions before selecting Symmetry Systems’ DataGuard. The other companies that the Crossbeam team looked at viewed data security from the outside in—that is, from the perimeter—to defend against attacks, rather than approaching security based on the attacker’s main objective—the data. For Crossbeam’s AWS cloud environment, DataGuard fit perfectly into their “security-from-the-data-out” ideology. Chris and the Crossbeam team saw the immediate benefit to a solution that offered improved data visibility, reduced data sprawl, and helped the Crossbeam security team prioritize their data security risks.
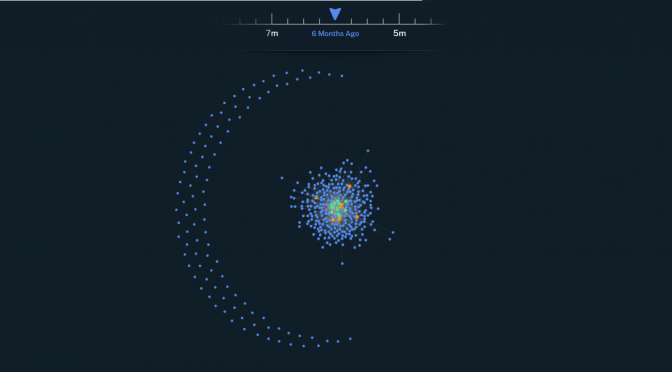
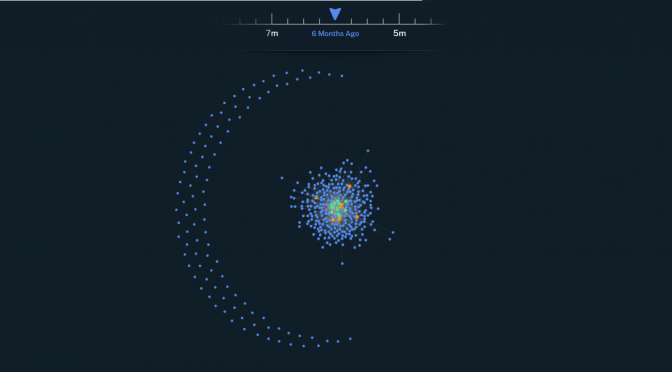
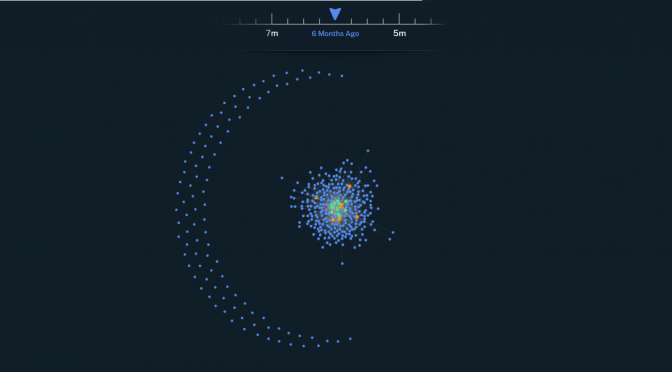
One of the greatest challenges DataGuard has solved for Crossbeam is the ability to see how data was being used and who was using it. Prior to deploying DataGuard, Crossbeam had no automated way to monitor data access and activity—everything was time and resource intensive. With DataGuard, Crossbeam can easily show auditors who accesses which data, how much privileged access they have, and if there are any errors in the data. The solution offers high, precise visibility into what is happening to the data.
After deployment and at the request of Crossbeam, Symmetry Systems used DataGuard to look for system weaknesses. According to Chris, during the test, the moment someone tried doing something they weren’t supposed to, DataGuard alerts for anomalous behavior were triggered, demonstrating DataGuard’s full capacity to actively and accurately protect the organization’s data.
About Symmetry
Symmetry is a pioneering Data+AI security platform engineered to conquer the most complex data security and privacy challenges across industries. Built on the foundation of innovation and backed by advanced AI technology, Symmetry delivers unparalleled data protection, ensuring total visibility and control over your data. Our solution empowers organizations to navigate regulatory landscapes, respond to emerging threats, and safeguard sensitive information with confidence and precision. Whether your focus is in finance, healthcare, manufacturing, or any other sector, Symmetry provides the tools you need to secure your data environment and drive your business forward. Join the ranks of the world’s most innovative companies that trust Symmetry to protect their most valuable assets.