Estimated reading time: 8 minutes
#TLDR
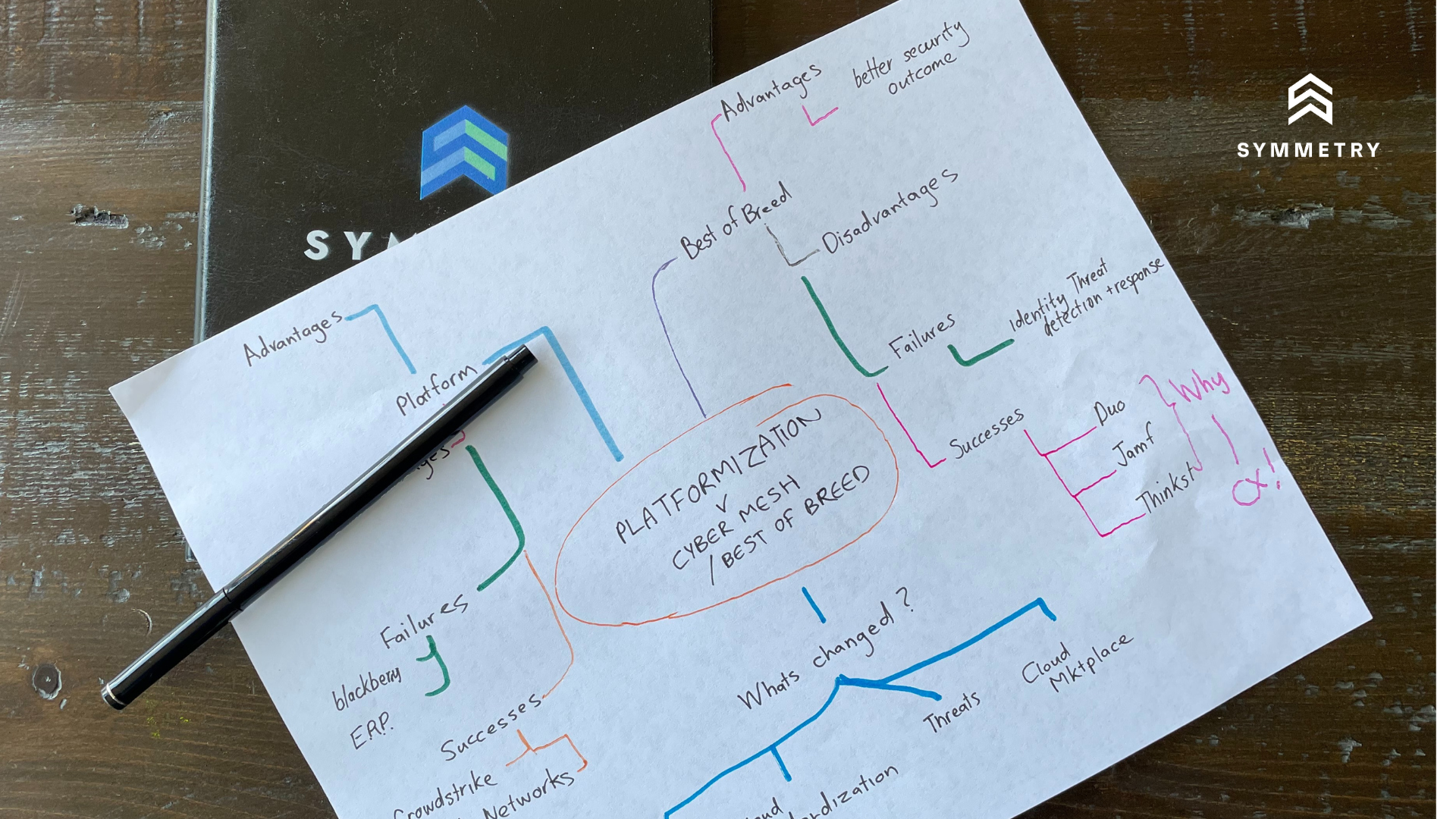
CISOs continually have to choose between best of breed security vs Platformization and further consolidation of vendors. The emergence of ERP tools presented a similar choice and most ERP projects have ended up as expensive failures. Open Integration is a better alternative today. Cloud providers are driving security products towards use of standardized interfaces, (encompassing findings, logs) and streamlined marketplaces (akin to app stores). Security data lakes and SIEM tools are at the forefront, enabling integrated “XDR” analytics. Increasingly, GenAI is seen as able to democratize the interpretation of data and analytics from best of breed tools for security engineers.
At Symmetry, we believe an integrated best of breed portfolio or “Cybersecurity Mesh” as Gartner refers to it will outperform Platformization in innovation and scale, much like a robust app store would outperform a single vendor mobile device with only the vendor’s applications.
CISOs should focus on how to maximize the value from your investment in security tools by understanding the overlaps, gaps and opportunities in your security capabilities; and where there are potential overlaps, evaluate the effectiveness of platforms and future investments in delivering the security outcomes needed right now – not future capability.
Introduction
CISOs increasingly think they face a pivotal choice between Best-of-Breed Vendors or a Security Platformization Strategy. Whether you refer to it as “Best-of-Breed vs. Best-in-Suite” or “Platform vs. Point Solution”, it is a debate that started in the ’90s with the advent of enterprise resource planning (ERP) software. There are clear advantages and disadvantages to either approach that are well documented as outlined in Note 1.1 The adoption of single vendor ERP platforms was likewise driven by the need to reduce complexity, leverage commonalities, unify data, and minimize management overhead.
A lot can and should therefore be learned from the failure of historical ERP deployments, where the onus was placed on the vendor to reduce the burden of integration across related systems.
Lessons Learned From ERP
Without doubt, ERP was the first real platformization approach – focusing on merging point solutions into a single platform. Before then, every back office application stood as a finely tuned point solution, meticulously designed for specific back-office tasks, be it accounts payable, payroll, or taxes. In the mid-’90s, ERP software emerged, integrating various complementary functions into a single solution and providing a unified insight to management. Customers were tired of trying to merge insights from across these systems themselves and looked to ERP platforms to solve this for them. While the theoretical benefits of tightly integrated ERP platforms are obvious, the practical realization often falls short.
Most ERP systems expanded capabilities through acquisitions, and likewise struggled to integrate themselves – leading to poorly digested integrations with more specialized systems with different code bases and often different approaches to data management. This resulted in serious integration and version-control issues, coupled with a user experience that frankly sucked. The exact same problems that platformization was attempting to address. Acquisitions that focused on code compatibility and similar data management were vastly more successful.
The approach to acquisition first and then engineering effort to enable the planned integration also had a profound impact on innovation—it essentially stifled it. Larger companies invested significant resources in post-acquisition and integration activities rather than innovating themselves, smaller more nimble companies continued to innovate independently and create more demand for M&A to keep pace. The cycle perpetuated, with promising smaller firms getting acquired and their creations attempted to be assimilated into the ERP offering.
The consequence of this acquisition and integration cycle was a set of ERP platforms that evolved into complex and costly platformization projects, posing significant challenges to manage and maintain with no choice to innovate, except through further acquisition.
What Has Changed Since Then?
Integration Has Become Easier
Since the advent of ERP systems, a confluence of technological advancements has laid a roadmap for better integration and adoption of best-of-breed solutions from multiple vendors. Central to this transformation is the widespread adoption of API-based architectures, providing standardized interfaces that facilitate seamless communication between diverse software applications. This has significantly alleviated interoperability challenges, allowing organizations to integrate specialized and innovative tools, including security with unprecedented ease.
Nowhere is the rate of innovation driven by open integration more noticeable than in the realm of mobile app stores. These ecosystems, flourishing under the influence of API-based architectures, exemplify the advantages of encouraging developers to build on standardized hardware with open integrations. Mobile app stores have become vibrant marketplaces where diverse applications, each excelling in its specialized domain, seamlessly converge. This approach contrasts starkly with the trajectory of companies like BlackBerry, which experienced a decline due to its initially closed ecosystem reliant solely on BlackBerry-designed apps at first. The contrast between these two models underscores the transformative power of fostering an environment that promotes collaboration, interoperability, and the integration of best-of-breed solutions from various developers, ultimately shaping a landscape rich in technological diversity and continuous advancement.
The introduction of generative AI has potential to further accelerate this process by expediting the understanding and integration of outputs from a spectrum of security solutions. AI algorithms now play a crucial role in interpreting and harmonizing data, fostering a cohesive and unified security ecosystem.
Standardization of Infrastructure
Moreover, the standardization of infrastructure-as-a-service (IaaS) capabilities, offered by hyperscale cloud providers like AWS, Azure, and GCP, has created a common ground for deploying and managing diverse best-of-breed solutions. These cloud providers not only offer standardized infrastructure but also leverage cloud marketplaces, streamlining the entire process from purchasing to implementation. Cloud marketplaces provide a centralized hub where organizations can discover, procure, and deploy a variety of security solutions. This streamlined approach not only simplifies the procurement process but also enhances the integration of best-of-breed tools into existing security architectures. In essence, these collective advancements empower organizations to build a dynamic and responsive security infrastructure that seamlessly combines the specialized strengths of individual solutions, all within the flexible and scalable environment offered by cloud platforms.
Dominant Security Platforms and Solutions Focus on Single Assets
You may very well argue that dominant security platforms have emerged in the security space, and platformization is the vendor strategy of choice. Security platforms like CrowdStrike, Snyk, Palo Alto Networks and Okta. But so have best-of-breed solutions like Duo or Thinkst Canary. The key to both? These successful platformization strategies have been most focused and most effective across asset layers as highlighted in Figure 1 below. Alternatively success has been found with integration of data from multiple layers to enable an integrated process flow and customer experience. There are clear leaders in each asset category, as a result.
Shifting Threat and Economic Landscape Focuses CISOs on Value
The contemporary threat landscape and economic outlook has obviously redefined the CISO’s challenge. CISOs need to focus more on optimizing the value of their cybersecurity spend than before. They are judged on the effectiveness in managed risk, in the face of pressure on budgets. The debate between single vendor or multi vendor approaches has really become less important than optimizing the investment. The question on most CISO’s minds is therefore where to focus their investment. At Symmetry, we believe that place is no longer on your perimeter network. Nor on your devices but where your most important asset “data” is at its most vulnerable “identity”.
The impact of the Shifting Landscape
It’s clear that this is no longer a debate between multi-vendor best-of-breed vs single vendor security platforms. A single unifying platform that is able to keep pace with the threat landscape not only seems unlikely. Instead judging by history of ERP and other single vendor platforms destined to quash innovation that cybersecurity desperately needs. Instead the focus should be on how to maximize the value from your investment in security tools. This requires CISOs to :
- delineate the lines between complementary, but slightly overlapping series of products/platforms to maximize the benefits of existing benefits using something like the Cyber Defence Matrix2
- Evaluate the effectiveness of platforms in delivering the security outcomes needed. Can it identify, protect, detect, respond and help recover from security threats to the asset layer it is protecting?
Along these lines, the integration between best of breed platforms emerges as the future, shaped across key asset layers. This shift is driven by the need to reduce complexity, leverage commonalities, and unified data, and minimizing management overhead. Technology consolidation spans multiple security capabilities, signaling a significant transformation in cybersecurity strategies.
Conclusion
It is clear that a lot has changed since the first ERP deployments that has transformed this decision from one designed to reduce the burden of technical integration on customers to one where CISOs can avail themselves of the best solutions with the same unified benefits of a single platform with less vendor lock-in and increased speed of innovation. These changes include:
- The emergence and use of API-based architectures and generative AI to enable seamless and easier integration across vendors;
- The standardization of underlying infrastructure and particularly data stores to make it easier to use common data models across applications;
- The emergence of dominant cybersecurity platforms focused on a more resilient approach to Cybersecurity rather than just prevention; and
- Shifting threat and economic environment putting greater emphasis on the value rather than just cost.
The outcome is clear to us. Focus on how to maximize the value from your investment in security tools by understanding the overlaps, gaps and opportunities in your security capabilities; and where there are potential overlaps, evaluate the effectiveness of platforms and future investments in delivering the security outcomes needed right now – not future capability.
- Note 1: The Advantages and Disadvantages
Best-of-Breed Security Solutions
Embracing a best-of-breed strategy presents organizations with compelling advantages, including the delivery of focused functionality and an enhanced user experience. This approach often boasts best-in-class capabilities, allowing organizations to select specialized tools that excel in addressing specific security challenges. The flexibility to replace products as needed adds an element of adaptability. However, deploying this strategy across every asset layer and security capability may introduce more complexities than it solves. The potential for interoperability challenges and significant overlap in capabilities could hinder the seamless integration of these specialized tools and require excess headcount. Furthermore, as the industry shifts towards a detection and response paradigm, managing a diverse array of best-of-breed products becomes more intricate, amplifying complexities, talent needs and costs associated with maintaining a patchwork of specialized solutions.
Single Vendor Security Platforms
Conversely, security platform vendors offer a contrasting approach with the promise of a unified and integrated security landscape. These platforms aim to alleviate interoperability challenges by consolidating various security functionalities under one umbrella. Additionally, the allure of lower Total Cost of Ownership (TCO) through bundled offerings enhances their appeal. However, this approach comes with its own set of considerations. The potential for vendor lock-in raises concerns about long-term adaptability and flexibility. Moreover, in the pursuit of a unified user experience, there might be compromises in specialized features. Organizations must carefully weigh the advantages of streamlined integration against the potential drawbacks of reduced flexibility and the need to conform to a one-size-fits-all security solution. There will always be gaps in capabilities provided by the platforms.
↩︎ - Note 2: Making Sense of it all with the Cyber Defense Matrix
Regardless of the approach, the Cyber Defense Matrix (CDM) (The brainchild of the ever impressive Sounil Yu) becomes an invaluable tool for assessing the need for best-of-breed solutions vs platforms. By leveraging the CDM, security professionals can discern the specific strengths and weaknesses within each domain, identifying areas where specialized tools may offer unparalleled advantages compared to coverage of existing platforms. This deliberate assessment helps organizations avoid unnecessary tool redundancy and ensures that each selected solution aligns with the unique requirements of the respective security layer.
Nevertheless, the nuanced landscape of the Cyber Defense Matrix also underscores potential challenges in the best-of-breed approach. The intricate interplay of capabilities across the Matrix may reveal instances of overlap, necessitating a careful balance between deploying specialized tools and avoiding redundancy. Striking this equilibrium requires a meticulous evaluation of the organization’s cybersecurity needs, weighing the benefits of focused functionality against the potential pitfalls of tool overlap.
As highlighted in Figure 1 above, the most effective platforms have been those focused across single asset layers or focused on integration of data from multiplier layers to enable an integrated process flow with broader context. ↩︎